Security Protection and Log Monitoring of ohpm-repo in HarmonyOS Next
In the HarmonyOS Next development environment, ohpm-repo serves as an important private repository, and its security cannot be underestimated. Effective security monitoring is a key means to safeguard the repository's security and prevent unauthorized access. Below, based on practical experience, I'll delve into how to achieve comprehensive security protection for ohpm-repo by analyzing security logs, setting up automatic alerts, and optimizing log storage. How to Analyze the Security Logs of ohpm-repo? ohpm-repo generates various types of logs, mainly including run.log, access.log, and operate.log. Each type of log contains different security information. A detailed analysis of these logs can help us detect potential security threats in a timely manner. run.log run.log records key information during the operation of ohpm-repo, such as service startup, shutdown, configuration loading, and various exception situations. When analyzing run.log, focus on log information at the error and warning levels. For example, if there are frequent records of database connection failures in the log, it may indicate that there is a problem with the database service or that the database configuration information has been modified. This could affect the normal operation of the repository and might even be a sign of an attack. By checking the specific error stack information, we can locate the exact code position where the problem occurred and then fix it. access.log access.log details all access requests to ohpm-repo, including the request time, source IP address, requested interface, and operation result. Analyzing access.log can help us identify abnormal access patterns. For instance, if an IP address initiates a large number of identical requests in a short period, it might be attempting a brute-force attack or a traffic spamming attack. Or if an abnormal IP address frequently tries to access sensitive interfaces, it could be an unauthorized access attempt. We can write scripts or use log analysis tools to statistically analyze and filter the access logs to find these abnormal access records. operate.log operate.log mainly records various user operations in ohpm-repo, such as logging in, publishing resource packages, and deleting packages. By analyzing operate.log, we can track user operation behaviors and ensure that all operations are legal and authorized. For example, if a user performs sensitive operations outside of working hours or a user frequently conducts deletion operations, there may be a risk of internal personnel violating regulations. Additionally, operation logs can be used for auditing and compliance checks to ensure that all operations comply with the enterprise's security policies. How to Set Up Automatic Security Alerts? To detect and respond to security incidents in a timely manner, we can combine tools like ELK (Elasticsearch, Logstash, Kibana) and Prometheus for anomaly detection and set up automatic security alerts. Anomaly Detection with ELK ELK is a powerful set of tools for log management and analysis. First, use Logstash to collect various log files of ohpm-repo and transfer them to Elasticsearch for storage and indexing. Then, create visual dashboards and alert rules in Kibana. For example, we can set an alert to be triggered when the number of requests from an IP address exceeds 100 within an hour. Kibana can send alert information to relevant security personnel via email, SMS, or instant messaging tools so that they can handle the situation promptly. Anomaly Detection with Prometheus Prometheus is an open-source monitoring and alerting system. We can integrate the Prometheus client into ohpm-repo to collect key performance indicators and status information. For example, collect indicators such as the number of database connections and request response times. Then, set alert rules in Prometheus. When an indicator exceeds a preset threshold, an alert is triggered. Alertmanager can be used to manage and send alert information to ensure that security personnel are notified in a timely manner. Best Practices: How to Optimize Log Storage and Ensure Audit Availability? As time passes, log files will continue to grow. This not only occupies a large amount of storage space but also affects the efficiency of log query and analysis. Therefore, optimizing log storage is crucial. Log Cleaning Regularly cleaning up expired log files is an effective approach. You can set the retention period for logs according to the enterprise's security policies and regulatory requirements. For example, set the retention period for run.log, access.log, and operate.log to three months. Log files that exceed this period can be automatically deleted. You can write scripts and combine them with the system's scheduled tasks (such as cron jobs) to achieve regular log cleaning. Compressed Storage Compressing log
In the HarmonyOS Next development environment, ohpm-repo serves as an important private repository, and its security cannot be underestimated. Effective security monitoring is a key means to safeguard the repository's security and prevent unauthorized access. Below, based on practical experience, I'll delve into how to achieve comprehensive security protection for ohpm-repo by analyzing security logs, setting up automatic alerts, and optimizing log storage.
How to Analyze the Security Logs of ohpm-repo?
ohpm-repo generates various types of logs, mainly including run.log, access.log, and operate.log. Each type of log contains different security information. A detailed analysis of these logs can help us detect potential security threats in a timely manner.
run.log
run.log records key information during the operation of ohpm-repo, such as service startup, shutdown, configuration loading, and various exception situations. When analyzing run.log, focus on log information at the error and warning levels. For example, if there are frequent records of database connection failures in the log, it may indicate that there is a problem with the database service or that the database configuration information has been modified. This could affect the normal operation of the repository and might even be a sign of an attack. By checking the specific error stack information, we can locate the exact code position where the problem occurred and then fix it.
access.log
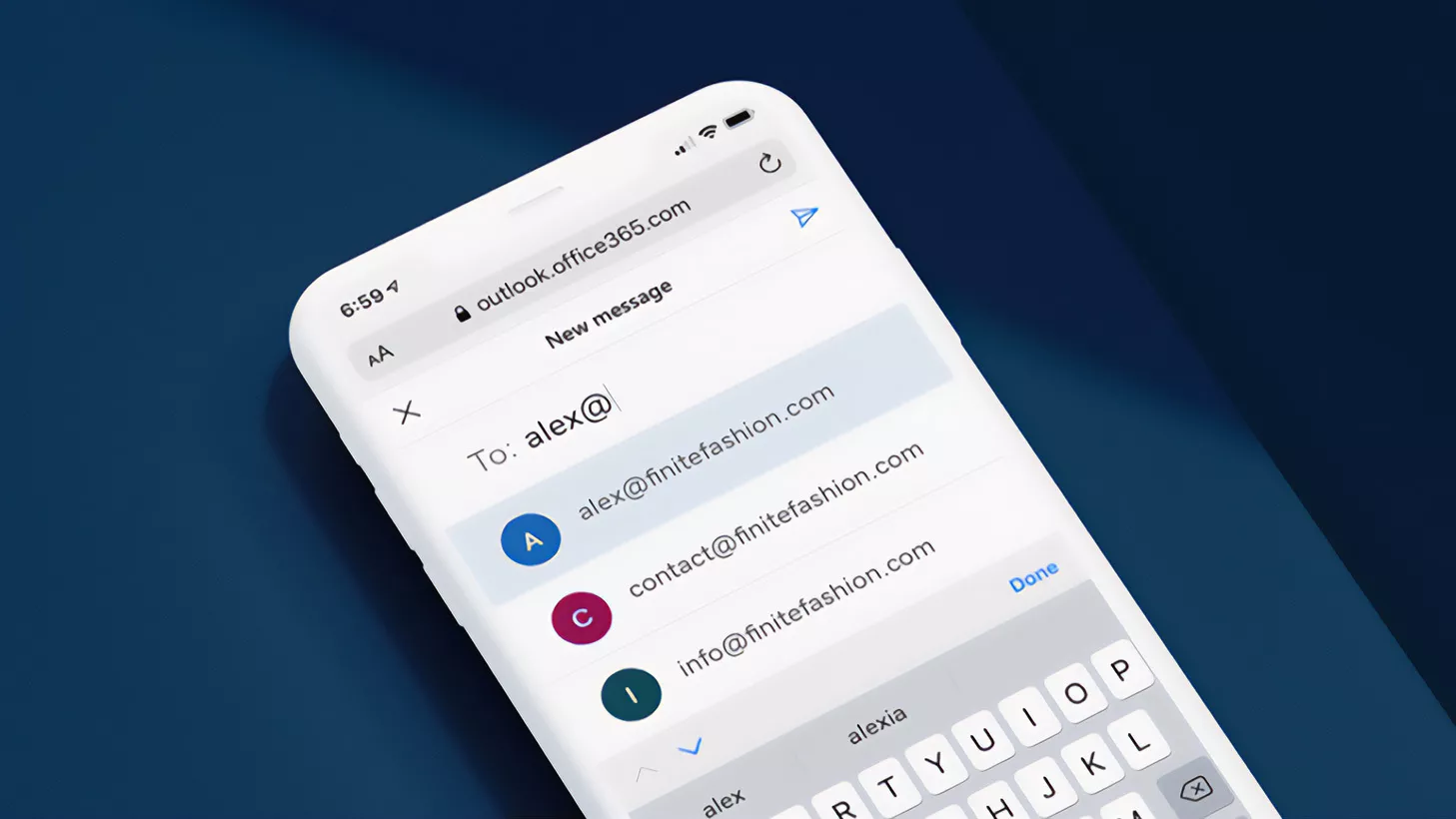
access.log details all access requests to ohpm-repo, including the request time, source IP address, requested interface, and operation result. Analyzing access.log can help us identify abnormal access patterns. For instance, if an IP address initiates a large number of identical requests in a short period, it might be attempting a brute-force attack or a traffic spamming attack. Or if an abnormal IP address frequently tries to access sensitive interfaces, it could be an unauthorized access attempt. We can write scripts or use log analysis tools to statistically analyze and filter the access logs to find these abnormal access records.
operate.log
operate.log mainly records various user operations in ohpm-repo, such as logging in, publishing resource packages, and deleting packages. By analyzing operate.log, we can track user operation behaviors and ensure that all operations are legal and authorized. For example, if a user performs sensitive operations outside of working hours or a user frequently conducts deletion operations, there may be a risk of internal personnel violating regulations. Additionally, operation logs can be used for auditing and compliance checks to ensure that all operations comply with the enterprise's security policies.
How to Set Up Automatic Security Alerts?
To detect and respond to security incidents in a timely manner, we can combine tools like ELK (Elasticsearch, Logstash, Kibana) and Prometheus for anomaly detection and set up automatic security alerts.
Anomaly Detection with ELK
ELK is a powerful set of tools for log management and analysis. First, use Logstash to collect various log files of ohpm-repo and transfer them to Elasticsearch for storage and indexing. Then, create visual dashboards and alert rules in Kibana. For example, we can set an alert to be triggered when the number of requests from an IP address exceeds 100 within an hour. Kibana can send alert information to relevant security personnel via email, SMS, or instant messaging tools so that they can handle the situation promptly.
Anomaly Detection with Prometheus
Prometheus is an open-source monitoring and alerting system. We can integrate the Prometheus client into ohpm-repo to collect key performance indicators and status information. For example, collect indicators such as the number of database connections and request response times. Then, set alert rules in Prometheus. When an indicator exceeds a preset threshold, an alert is triggered. Alertmanager can be used to manage and send alert information to ensure that security personnel are notified in a timely manner.
Best Practices: How to Optimize Log Storage and Ensure Audit Availability?
As time passes, log files will continue to grow. This not only occupies a large amount of storage space but also affects the efficiency of log query and analysis. Therefore, optimizing log storage is crucial.
Log Cleaning
Regularly cleaning up expired log files is an effective approach. You can set the retention period for logs according to the enterprise's security policies and regulatory requirements. For example, set the retention period for run.log, access.log, and operate.log to three months. Log files that exceed this period can be automatically deleted. You can write scripts and combine them with the system's scheduled tasks (such as cron jobs) to achieve regular log cleaning.
Compressed Storage
Compressing log files can significantly reduce storage space usage. Common compression tools like gzip or bzip2 can be used to compress log files. During compression, you can choose to compress them by time period, such as compressing the log files of the current day or week daily or weekly. In this way, when querying historical logs, you can first decompress the corresponding compressed files.
Data Retention Policy
Formulating a reasonable data retention policy can ensure that storage space usage is minimized while meeting audit requirements. In addition to retention based on time, hierarchical storage can also be implemented according to the importance of logs. For example, retain error and warning-level logs for a longer time, while retaining ordinary access logs for a shorter time. At the same time, important log data can be backed up to external storage devices or cloud storage to prevent data loss.
Through in-depth analysis of ohpm-repo security logs, setting up automatic security alerts, and optimizing log storage, we can build a comprehensive security monitoring system to effectively prevent unauthorized access and ensure the secure and stable operation of ohpm-repo. In practical applications, these measures should be flexibly adjusted and improved according to the specific needs and security situation of the enterprise.




































/https://tf-cmsv2-smithsonianmag-media.s3.amazonaws.com/filer_public/a6/73/a673143a-c068-4f51-a040-6d4f37d601c0/gettyimages-1124673966_web.jpg?#)