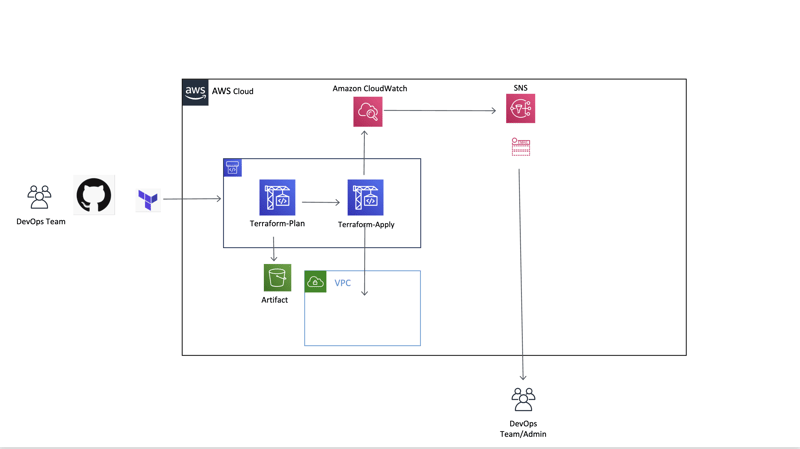
Secure Your AWS Pipeline: Step-by-Step Guide to VPC Integration-part 2
Welcome back! I hope you still have an appetite for learning more about CICD and how to secure your deployments. In Part 1, you built your first AWS CICD pipeline. Awesome job, but as any great chef knows, it’s not just about making a delicious dish; you must also keep your kitchen organized and safe. Now that your pipeline is up and running, it’s time to take the next step: securing access to your private resources within a VPC and setting up proper permissions. In this part, we’ll cover: What is a VPC and why does it matter? How to securely connect your pipeline to a production environment in a private subnet? Let’s dive right in!
Welcome back!
I hope you still have an appetite for learning more about CICD and how to secure your deployments. In Part 1, you built your first AWS CICD pipeline. Awesome job, but as any great chef knows, it’s not just about making a delicious dish; you must also keep your kitchen organized and safe.
Now that your pipeline is up and running, it’s time to take the next step: securing access to your private resources within a VPC and setting up proper permissions.
In this part, we’ll cover:
- What is a VPC and why does it matter?
- How to securely connect your pipeline to a production environment in a private subnet?









![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)