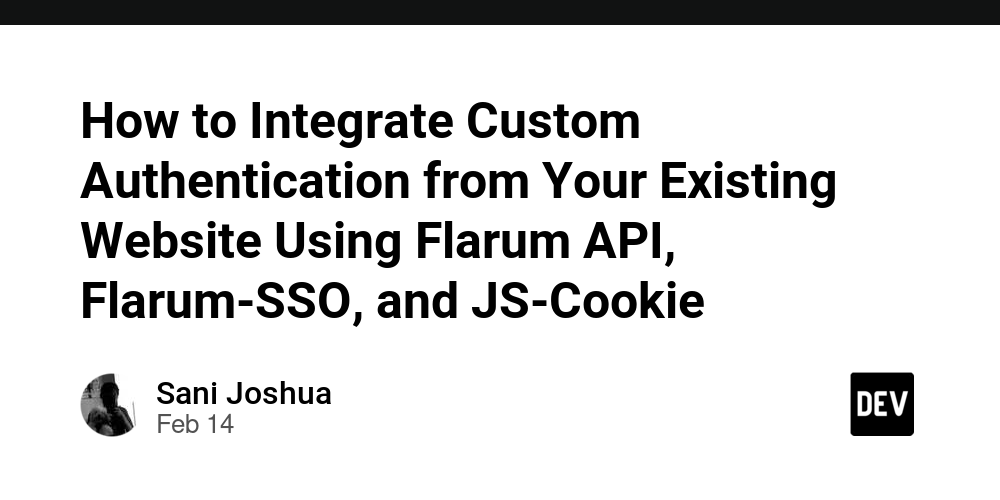
Microsoft March 2025 Patch Tuesday: Fixes for 57 Vulnerabilities & 6 Actively Exploited Zero-Days
Microsoft’s March 2025 Patch Tuesday addresses 57 vulnerabilities, including six zero-day vulnerabilities that are currently being exploited. The security update includes fixes for Windows, Microsoft Office, Azure, and other components. The March patch tuesday update included fixes for: In addition to the zero-day flaws, this Patch Tuesday includes fixes for: Zero-Day Vulnerabilities A zero-day vulnerability […] The post Microsoft March 2025 Patch Tuesday: Fixes for 57 Vulnerabilities & 6 Actively Exploited Zero-Days appeared first on Cyber Security News.

Microsoft’s March 2025 Patch Tuesday addresses 57 vulnerabilities, including six zero-day vulnerabilities that are currently being exploited. The security update includes fixes for Windows, Microsoft Office, Azure, and other components.
The March patch tuesday update included fixes for:
In addition to the zero-day flaws, this Patch Tuesday includes fixes for:
- 23 Elevation of Privilege Vulnerabilities
- 3 Security Feature Bypass Vulnerabilities
- 23 Remote Code Execution Vulnerabilities
- 4 Information Disclosure Vulnerabilities
- 1 Denial of Service Vulnerabilities
- 3 Spoofing Vulnerabilities
Zero-Day Vulnerabilities
A zero-day vulnerability is one that is actively exploited or publicly disclosed before an official patch is available1. This month’s Patch Tuesday addresses six actively exploited zero-day flaws and one that has been publicly exposed1.
The actively exploited zero-day vulnerabilities included in today’s updates are:
- CVE-2025-24983 – Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability This vulnerability allows a local attacker to gain SYSTEM privileges on a device after winning a race condition. Filip Jurčacko reported it from ESET, who found that the exploit was deployed via the PipeMagic backdoor and targeted older Windows versions, such as Windows 8.1 and Server 2012 R2. The vulnerability is also present in newer Windows OS versions, including Windows 10 build 1809 and Windows Server 2016.
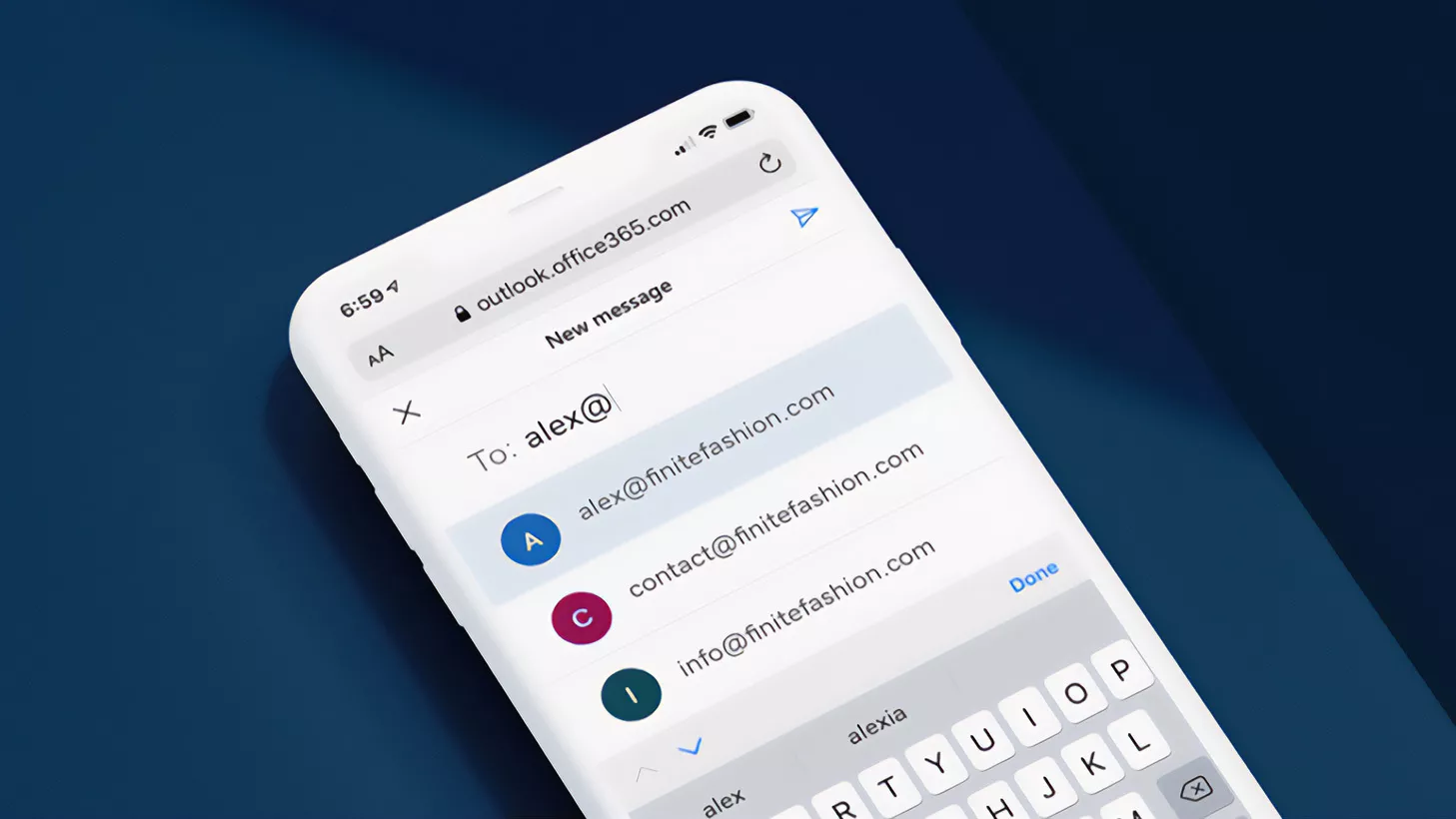
- CVE-2025-24984 – Windows NTFS Information Disclosure Vulnerability Attackers with physical access to a device can exploit this vulnerability by inserting a malicious USB drive to read portions of heap memory and steal information.
- CVE-2025-24985 – Windows Fast FAT File System Driver Remote Code Execution Vulnerability This vulnerability is a combination of integer overflow and heap-based buffer overflow defects in the Windows Fast FAT File System Driver.
- CVE-2025-24991 – Windows NTFS Information Disclosure Vulnerability
- CVE-2025-24993 – Windows NTFS Remote Code Execution Vulnerability An attacker could exploit these vulnerabilities by tricking a target into mounting a malicious virtual hard disk, which could lead to local code execution or disclosure of memory contents.
- CVE-2025-26633 – Microsoft Management Console Security Feature Bypass Vulnerability Exploitation requires user interaction, where an attacker must convince a user to click a malicious link or open a malicious file to circumvent security restrictions and gain unauthorized access to administrative tools or system settings.
Other Important Vulnerabilities
Some of the critical vulnerabilities that have been fixed this month include:
- CVE-2025-24045 and CVE-2025-24035 These are two critical vulnerabilities in Windows Remote Desktop Services (RDS). An attacker could exploit these vulnerabilities by connecting to a system with the Remote Desktop Gateway role, triggering a race condition to create a use-after-free scenario, and then leveraging this to execute arbitrary code.
- CVE-2025-24044 – Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerabilities A local, authenticated attacker would need to win a race condition in order to exploit this vulnerability. Successful exploitation of the vulnerability would allow the attacker to gain SYSTEM privileges.
- CVE-2025-24064 – Windows Domain Name Service Remote Code Execution Vulnerability
- CVE-2025-24084 – Windows Subsystem for Linux (WSL2) Kernel Remote Code Execution Vulnerability
Given the number of actively exploited vulnerabilities, system administrators must apply these patches as soon as possible to protect their systems from potential attacks.
Are you from SOC/DFIR Teams? – Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Microsoft March 2025 Patch Tuesday: Fixes for 57 Vulnerabilities & 6 Actively Exploited Zero-Days appeared first on Cyber Security News.




































/https://tf-cmsv2-smithsonianmag-media.s3.amazonaws.com/filer_public/a6/73/a673143a-c068-4f51-a040-6d4f37d601c0/gettyimages-1124673966_web.jpg?#)