Hackers Leveraging DNS MX Records To Dynamically Create Fake Logins Mimic as 100+ Brands
A sophisticated phishing operation has emerged that creatively leverages DNS mail exchange (MX) records to dynamically serve fake login pages tailored to victims’ email providers. The attack can mimic over 100 brands and represents a significant evolution in phishing techniques, creating highly convincing impersonations that are difficult for users to distinguish from legitimate login pages. […] The post Hackers Leveraging DNS MX Records To Dynamically Create Fake Logins Mimic as 100+ Brands appeared first on Cyber Security News.

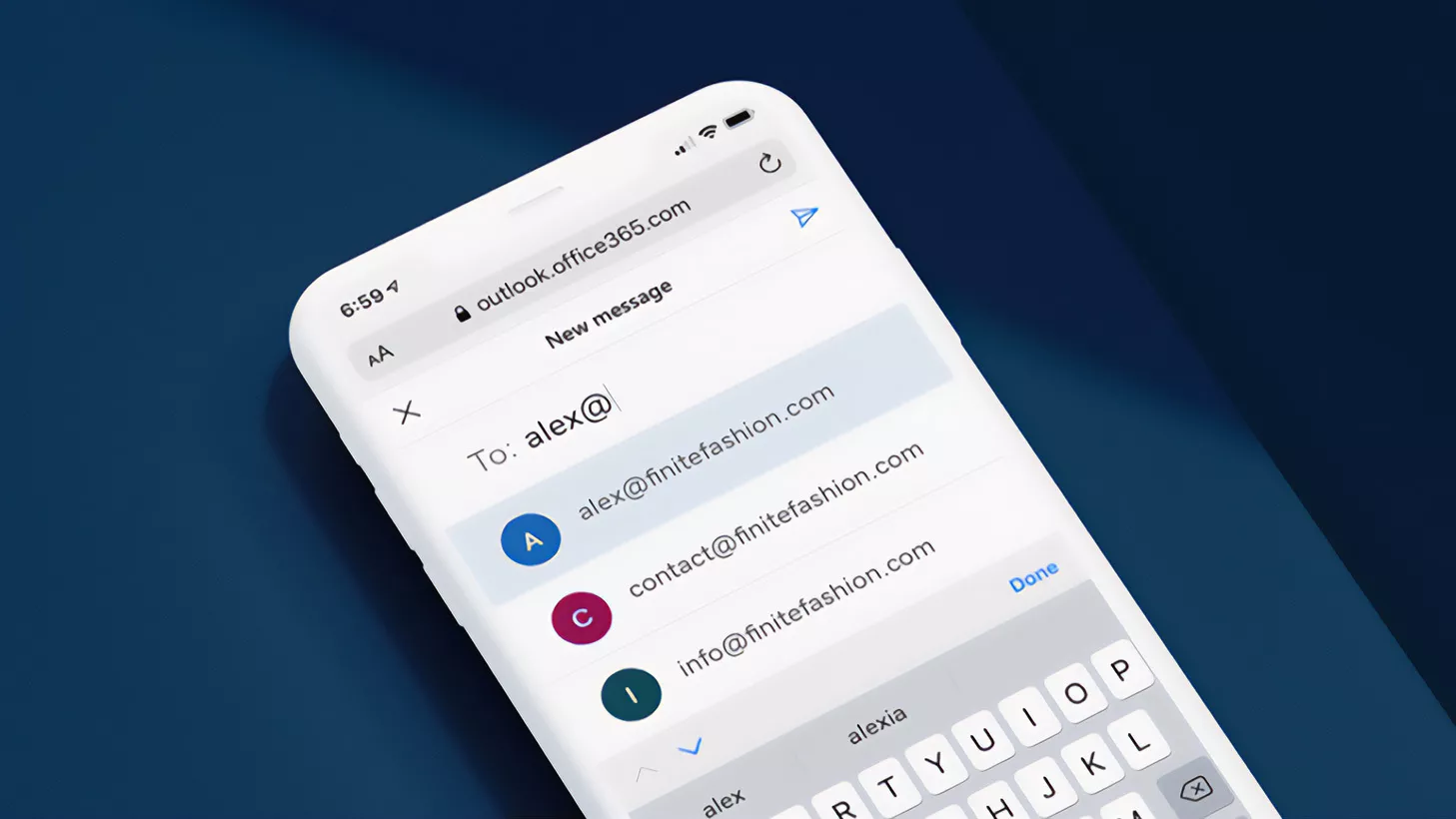
A sophisticated phishing operation has emerged that creatively leverages DNS mail exchange (MX) records to dynamically serve fake login pages tailored to victims’ email providers.
The attack can mimic over 100 brands and represents a significant evolution in phishing techniques, creating highly convincing impersonations that are difficult for users to distinguish from legitimate login pages.
The threat begins with spam emails containing malicious links that redirect victims through a series of steps to the phishing landing page.
.webp)
These emails typically employ urgent messaging around account deactivation or document delivery, compelling users to click embedded hyperlinks.
The links often point to compromised WordPress websites, fraudulent accounts on free web hosting services, or exploit open redirects on advertising networks to bypass email security systems.
Infoblox researchers identified the threat actor behind this operation as “Morphing Meerkat,” which appears to operate a sophisticated Phishing-as-a-Service (PhaaS) platform.
.webp)
This assessment is based on consistent tactics, techniques, and procedures observed across multiple campaigns dating back to January 2020. The operation has maintained core infrastructure while continuously evolving its capabilities.
Technical implementation
What makes this campaign particularly dangerous is its ability to serve one of 114 different brand-specific phishing templates based on the victim’s email domain.
The phishing kit performs a DNS MX record lookup using DNS over HTTPS (DoH) services from Google or Cloudflare, allowing it to precisely identify the victim’s email service provider without maintaining an extensive domain mapping database.
The technical implementation relies on JavaScript functions that query public DNS services, as seen in this code snippet from the phishing kit:-
async function getMXRecord(domain) {
try {
const response = await fetch(`https://dns.google/resolve?name=${domain}&type=MX`);
const data = await response.json();
if (data && data.Answer && data.Answer.length > 0) {
const mxRecords = data.Answer.map(record => `${record.data}`).join('\n');
return mxRecords;
} else {
return 'no-mx';
}
} catch (error) {
return 'MX-Error';
}
}The phishing kit then maps the returned MX record to a matching phishing template, automatically filling the username field with the victim’s email address.
If the victim submits their credentials, the data is exfiltrated to the attackers via email, PHP scripts, AJAX requests, or messaging platforms like Telegram.
To evade detection, the kit employs multiple security techniques, including code obfuscation, keyboard monitoring to prevent inspection, and intelligent redirects to legitimate websites after credential theft.
The post Hackers Leveraging DNS MX Records To Dynamically Create Fake Logins Mimic as 100+ Brands appeared first on Cyber Security News.