Hackers Abuse COM Objects for Fileless Malware Lateral Movements
A sophisticated technique was recently detected by researchers where attackers abuse Component Object Model (COM) objects to execute fileless malware for lateral movement across networks. This technique, detailed in research from March 2025, leverages legitimate Windows functionality to establish persistence and evade traditional security controls, marking a significant evolution in attack methodologies. The attack exploits […] The post Hackers Abuse COM Objects for Fileless Malware Lateral Movements appeared first on Cyber Security News.

A sophisticated technique was recently detected by researchers where attackers abuse Component Object Model (COM) objects to execute fileless malware for lateral movement across networks.
This technique, detailed in research from March 2025, leverages legitimate Windows functionality to establish persistence and evade traditional security controls, marking a significant evolution in attack methodologies.
The attack exploits the Component Object Model (COM), a binary interface standard developed in the early 1990s that remains integral to modern Windows operating systems.
COM enables distinct, modular components to interact with applications regardless of the underlying programming language, providing essential functionality that makes it an attractive target for malicious actors.
IBM analysts identified that this attack methodology builds upon research from James Forshaw of Google Project Zero, who in February 2025 detailed a novel approach for abusing Distributed COM (DCOM) remoting technology.
The technique allows trapped COM objects to execute .NET managed code within the context of server-side DCOM processes, potentially leading to privilege escalation and Protected Process Light (PPL) bypass.
Security researchers Dylan Tran and Jimmy Bayne subsequently expanded on this approach to develop a proof-of-concept demonstrating fileless lateral movement capabilities.
Their research showcases how attackers can leverage DCOM to remotely manipulate registry settings and execute malicious code without leaving obvious artifacts on disk.
The technique’s potency stems from its ability to operate within legitimate Windows processes, specifically targeting the WaaSMedicSvc service that executes within a protected svchost.exe process with SYSTEM privileges.
Infection Mechanism
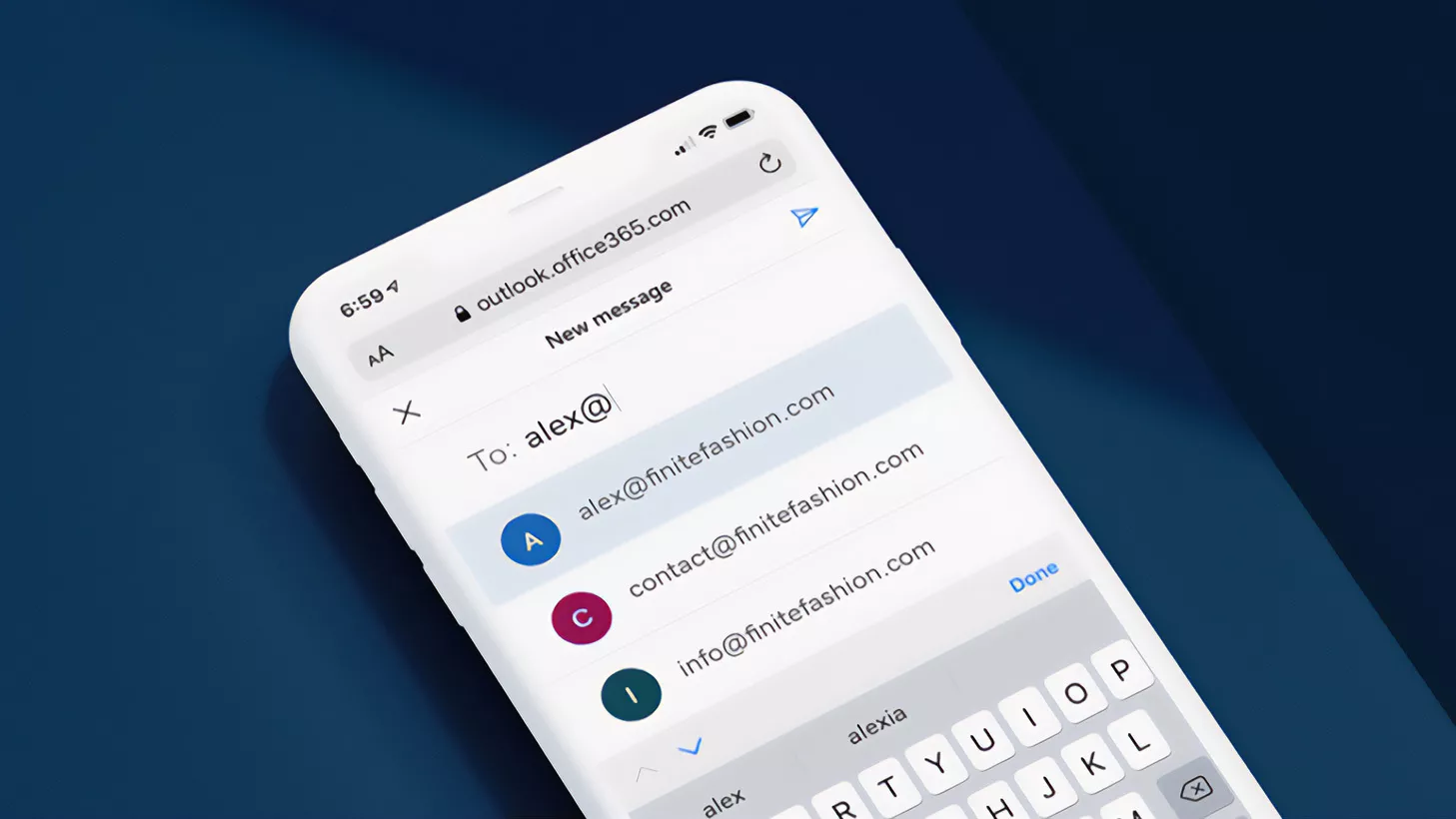
The attack begins with manipulation of remote registry settings to enable .NET reflection over DCOM by setting AllowDCOMReflection and OnlyUseLatestCLR values in the target’s HKLM\Software\Microsoft.NetFramework registry path.
.webp)
Attackers then exploit COM hijacking by modifying the TreatAs key of the StandardFont CLSID, redirecting execution flow.
When implemented, the technique allows attackers to execute a sequence similar to:-
// Parent array -- object[] {}
SAFEARRAY* psa;
SAFEARRAYBOUND rgsabound[1];
rgsabound[0].lLbound = 0;
rgsabound[0].cElements = 1;
psa = SafeArrayCreate(VT_VARIANT, 1, rgsabound);This allows for dynamic loading of malicious .NET assemblies via Assembly.Load over DCOM, with execution occurring entirely in memory within a Protected Process Light svchost.exe context.
The malware resides exclusively in memory, making traditional file-based detection ineffective.
Security professionals recommend monitoring for CLR load events within svchost.exe processes, detecting registry manipulations of specific COM-related keys, and implementing host-based firewall restrictions to mitigate this emerging threat vector.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post Hackers Abuse COM Objects for Fileless Malware Lateral Movements appeared first on Cyber Security News.








![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)